Privacy Audit Tools Write For Us

We review the best network security monitoring tools to monitor for potential network threats, fix problems, and discover vulnerabilities before they become problems.
It can also give you an overview of the network, which can be helpful when trying to troubleshoot specific issues. Security audits can also help you understand how well your organization is protected against known security fears.
we take a look at the top net security monitoring tools, including port scanners, vulnerability scanners, patch managers, and more, to help you scan your network for security issues and fix vulnerabilities.
What are the key features to look for in privacy audit tools?
When selecting data privacy audit tools, look for features such as comprehensive data mapping, compliance checklists, automated reporting, and user-friendly dashboards. Additionally, ensure the tool supports multiple regulations like GDPR and CCPA, offers risk assessment capabilities, and provides integration with existing systems to streamline your privacy management processes.
Here is our list of the best network security audit tools:
- Tufin Orchestration Suite EDITOR’S PICK This SaaS platform creates security systems for hybrid networks to protect connections and applications while ensuring compliance with stringent legal obligations set by PIPL, CSL, and DSL, and helping professionals achieve the necessary certification designation from the American Bar Association. This service monitors newly employed security rules and then monitors the network to verify them while logging all actions and responses for security verification, including the latest developments and new content in security protocols. Access a demo.
- SolarWinds Network Configuration Manager (FREE TRIAL) Our #1 choice for network security monitoring. Configuration management tool with vulnerability scans, reports, alerts, and resources from the Westin Research Center. Download a free 30-day trial.
- Intruder (FREE TRIAL) A cloud-based vulnerability scanner with monthly scans, on-demand scans, and the services of a penetration testing team.
- ManageEngine Vulnerability Manager Plus (FREE TRIAL) This system security verification package scans your network and looks for security vulnerabilities. It works on Windows and Windows Server.
- ManageEngine Log360 (FREE TRIAL) A SIEM package that collects logs from network endpoints and cloud platforms and stores them for compliance audits, ensuring it complies with applicable state laws. It works on windows server.
- ManageEngine Log360 (FREE TRIAL) A SIEM package that collects logs from network endpoints and cloud platforms and stores them for compliance audits. It works on windows server.
- Netwrix Auditor AI Network security audit software with configuration monitoring, automatic alerts and other APIs.
- Netwrix Auditor Network security audit software with configuration monitoring, automatic alerts and other APIs.
- Nessus Free Vulnerability Assessment Tool with 450+ configuration templates and customizable reports.
- Nmap Open source port scanner and network mapper available as CLI or GUI (Zenmap).
- OpenVAS vulnerability assessment tool for Linux users with regular updates.
- Acunetix A web application security scanner capable of detecting over 50,000 network liabilities when joined with OpenVAS.
- Kaseya VSA RMM software with IT asset detection, custom dashboards, reporting and robotics.
- Spiceworks Inventory A free web-based system IT asset management tool that mechanically discovers network devices through an on-site agent.
- Network Inventory Advisor inventory scanning tool compatible with Windows, Mac OS and Linux devices.
- Metasploit penetration testing tool that allows you to hack exploits on your network.
How to Submit Your Articles
For Submitting Your Articles, you can email us at contact@supercomputerworld.com
Why Write For Super Computer World – Privacy Audit Tools Write For Us

Search Related Terms to Privacy Audit Tools Write For Us
Productivity Software
Spreadsheets, Word Processors
Specialized Software
Audit across North America
Information Security
Information Technology Security Audit
Disaster Recovery
Risk Management
Information Technology Audit
Organization Chart
Operating Systems
Software Applications
Change Management
Physical Security
Information Systems Audit And Control Association (Isaca)
Disaster Recovery Plan
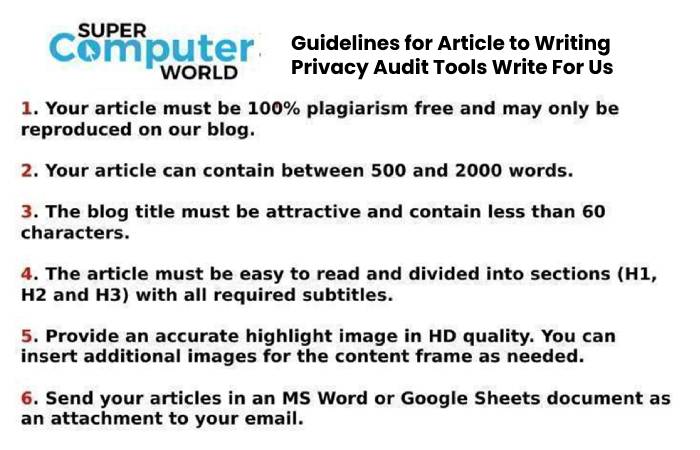
Guidelines for Article to Writing Privacy Audit Tools Write For Us